As a system architect, it's crucial to design systems that are secure, scalable, and efficient. One fundamental component of modern architectures is the proxy server, which serves as an intermediary between clients and backend services.
A proxy server can enhance performance, security, and manageability by intercepting requests and modifying or forwarding them. Two major types of proxies used in system design are:
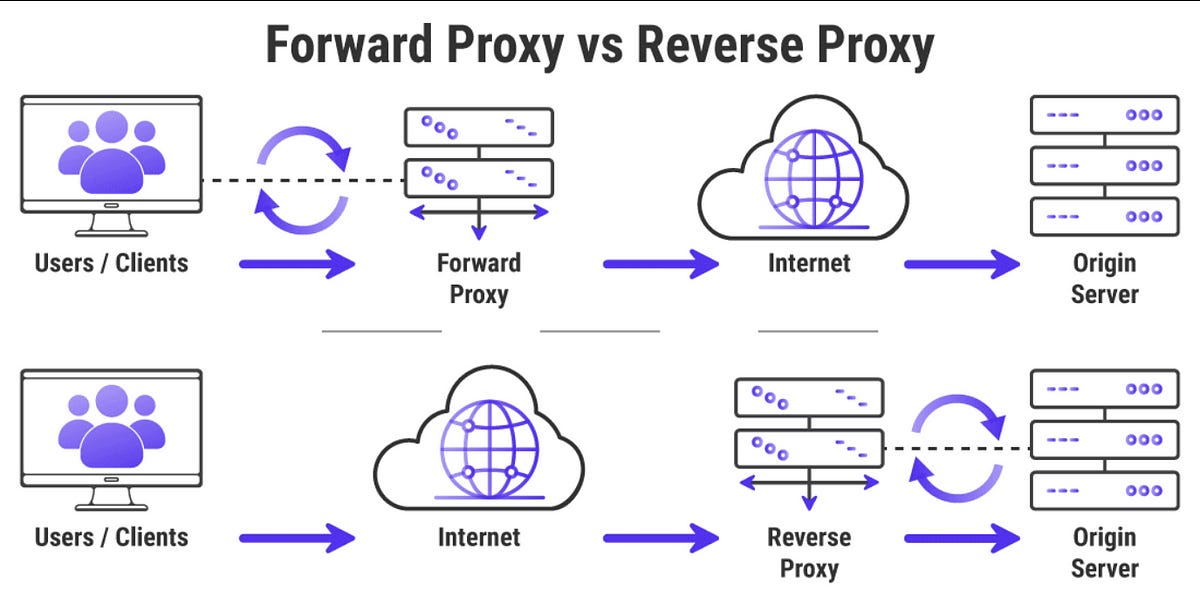
Forward Proxy – Used for handling outbound traffic from clients to external servers.
Reverse Proxy – Used for managing inbound traffic to backend servers.
Additionally, many people confuse proxy servers with VPNs, firewalls, and load balancers. This article covers everything a system architect should know, including advantages, disadvantages, and key differences between these technologies.
What is a Proxy Server?
A proxy server sits between a client and a destination server. Instead of the client directly connecting to the target server, its request is routed through the proxy. The proxy can:
✅ Modify requests (e.g., filtering specific content).
✅ Cache responses for faster performance.
✅ Mask IP addresses for anonymity.
✅ Enhance security by blocking malicious traffic.
Depending on whether the proxy is serving clients or backend servers, it functions as either a forward proxy or a reverse proxy.
1. Forward Proxy (Client-Side Proxy)
A forward proxy (or simply proxy server) sits between clients and the internet, handling all outgoing requests on behalf of users.
How Forward Proxy Works
A client requests data from an external website or service.
The forward proxy receives and modifies (if necessary) the request.
The proxy forwards the request to the target server.
The server responds, and the proxy relays the response back to the client.
Common Use Cases of Forward Proxy
Privacy & Anonymity: Masks the client's IP address to prevent tracking.
Content Filtering: Used in schools or offices to block access to specific websites.
Security: Prevents malware and cyber threats from affecting internal clients.
Caching: Reduces bandwidth usage and speeds up frequently accessed web pages.
Examples of Forward Proxy in Use
Squid Proxy – Used for caching and content filtering.
Tor Network – Enables anonymous browsing by routing traffic through multiple nodes.
Corporate Proxy Servers – Block or log access to restricted websites.
Advantages of Forward Proxy
✔️ Improves privacy and security by masking user IPs.
✔️ Helps bypass geo-restrictions on content.
✔️ Reduces network congestion with caching.
Disadvantages of Forward Proxy
❌ Can slow down requests if the proxy is overloaded.
❌ Certain websites can detect and block proxies.
❌ A compromised proxy can track or intercept sensitive data.
2. Reverse Proxy (Server-Side Proxy)
A reverse proxy sits between external clients and backend servers, intercepting all incoming requests before they reach backend services.
How Reverse Proxy Works
A client sends a request to the reverse proxy instead of the backend server.
The reverse proxy decides which backend server should handle the request.
The backend processes the request and returns the response to the proxy.
The proxy relays the response to the client, often with optimizations like compression or caching.
Common Use Cases of Reverse Proxy
Load Balancing: Distributes traffic across multiple backend servers to prevent overloading.
DDoS Protection: Filters out malicious traffic before it reaches backend systems.
SSL Termination: Offloads SSL encryption/decryption to improve server performance.
Caching & Compression: Reduces response times by serving cached data.
Examples of Reverse Proxy in Use
NGINX & HAProxy – Used for load balancing and caching.
Cloudflare & AWS CloudFront – Reverse proxies that protect web applications from attacks.
Varnish – Caching reverse proxy for high-speed web applications.
Advantages of Reverse Proxy
✔️ Enhances security by hiding backend IP addresses.
✔️ Improves scalability by handling load distribution.
✔️ Reduces latency through caching and request optimization.
Disadvantages of Reverse Proxy
❌ A single point of failure if not configured with redundancy.
❌ May add latency if improperly optimized.
❌ Needs additional setup and maintenance.
Key Differences: Proxy vs VPN, Firewall, and Load Balancer
1. Proxy vs VPN
Both proxies and VPNs help hide a user's identity, but a VPN provides a higher level of security.
A proxy only masks your IP address and may cache or filter content.
A VPN encrypts all traffic between your device and the VPN server, making it much harder for ISPs or hackers to intercept data.
Proxies work per-application (e.g., web browsers), whereas VPNs encrypt all network traffic.
Use a proxy for bypassing geo-blocks or content filtering. Use a VPN for privacy, security, and encrypted communication.
2. Proxy vs Firewall
A firewall is a security mechanism that monitors and controls incoming and outgoing traffic based on predefined rules.
A proxy routes traffic but doesn't actively block malicious activity like a firewall.
Firewalls operate at multiple layers (network, transport, application), whereas proxies mostly function at the application level.
A firewall acts like a border checkpoint—blocking unauthorized traffic. A proxy is more like a middleman—intercepting and modifying requests.
Use a firewall to block security threats. Use a proxy to optimize traffic flow and manage requests.
3. Proxy vs Load Balancer
A load balancer is designed to distribute incoming traffic across multiple servers, ensuring high availability and performance.
A reverse proxy also handles incoming requests but focuses on security, caching, and optimization.
A load balancer ensures no single server gets overloaded.
Some technologies, like NGINX and HAProxy, act as both a reverse proxy and a load balancer, depending on the configuration.
Use a reverse proxy to secure and optimize traffic. Use a load balancer to distribute requests efficiently.
Final Thoughts
As a system architect, knowing when and how to use proxies can significantly impact your system's scalability and security.
✅ Use a forward proxy if you need to control outbound requests, enforce access restrictions, or improve privacy.
✅ Use a reverse proxy to protect backend servers, balance load, and optimize performance.
✅ Differentiate between proxies, VPNs, firewalls, and load balancers to build a well-secured and optimized system.
By effectively integrating proxy servers, VPNs, firewalls, and load balancers, you can enhance security, improve speed, and ensure system reliability. 🚀
Would you like a deep dive into specific proxy implementations? Let me know in the comments!